Program Overview
In an era dominated by technology, the threats of malware, spyware, ransomware, and cyber attacks loom large. The consequences can be devastating, costing businesses millions or even billions. It's time to equip yourself with the knowledge to combat these threats through our PGP in Cyber Security certification at Digicrome.
Program Highlights:
Our PGP in Cyber Security is crafted to educate learners on comprehensive approaches to secure and protect data, safeguarding IT structures from potential harm. This online training program emphasizes skill-building for the real cyber world, covering data protection, risk analysis, cloud-based security, and compliance.
Why Choose Digicrome's PGP in Cyber Security?
Comprehensive Curriculum: Our meticulously designed curriculum offers a natural progression, introducing learners to interconnected facets of cybersecurity, including risk reduction, cloud security, and compliance.
Expert Faculty: Delivered by industry leaders, our immersive lectures leverage advanced technological tools for a rich learning experience. Dedicated program managers address non-curricular queries and manage course aspects.
Hands-on Learning: Assignments and projects are integral to the program, allowing you to test and apply newly acquired knowledge constructively. Instructors provide detailed feedback, fostering active participation.
Networking Opportunities: Our platform facilitates learner networking, connecting you with peers, mentors, and industry professionals through email, voice calls, and video calls, enhancing the online learning experience.
Flexible Support: One-on-one doubt-clearing sessions, coupled with email, voice call, and video call support, ensure a smooth learning journey. The dedicated support system covers study material-related doubts and managerial queries.
Why PGP in Cyber Security?
The PGP in Cyber Security course is in high demand as professionals seek to understand and combat cyber threats that can potentially dismantle a technology-driven world. At Digicrome, we design our course to impart skills that align with industry demands, preparing you for top-paying jobs in the sector.
Key Skills Covered:
- Authentication
- Identification
- Internet Governance
- Cyber Threats, Warfare, Crime, and Terrorism
- Cyber Security Policies
- International Convention on Cyberspace
- Nodal Authority
Objective of PGP in Cyber Security Certification Training:
The course aims to introduce students to various cyber-attacks, countermeasures, cyber threats, detection, protection of infrastructure, and understanding of Information Security (INFOSEC) and Denial-Of-Service Attacks (DOS).
Requirements:
- Graduate with a relevant background, scoring a minimum of 50%.
- No upper age limit.
- Minimum of 2 years of working experience in the same domain.
Benefits of PGP in Cyber Security Training Online at Digicrome:
- Better Career Scope
- Job Security
- High Salary
- Emerging Leadership Skills
- Financial Motivation and Incentives
- Hands-on Exposure to Practical Projects
- Solving Complex Industry Problems
- Working on Various Case Studies
- Bettering Career Support and Industry Exposure
Embark on a transformative journey with Digicrome's PGP in Cyber Security certification. Gain a competitive edge in the ever-evolving field of cybersecurity and fortify your career prospects as an expert in the realm of cyber threats.
Post Graduate Program In Cyber Security
- ₹70000.00
Features
- 06-Months Online Program
- Multiple Live Projects
- Career Assistance Guarantee
- Live Online Sessions
Key Highlights
 06-Months Online Program
06-Months Online Program Multiple Live Projects
Multiple Live Projects Career Assistance Guarantee
Career Assistance Guarantee
 Live Online Sessions
Live Online Sessions
 Expert Experienced Trainers
Expert Experienced Trainers
 1:1 Doubt Session
1:1 Doubt Session
 Learning Management System
Learning Management System
 24*7 Career Support
24*7 Career Support
Program Objective
- Introduction of PGP Cyber Security Program
- What is Cybersecurity?
- The Importance of Cybersecurity
- Why is Cybercrime Increasing?
- What is the Impact of Cybercrime?
- How to Protect your Organization Against Cybercrime?
- Examples of Damages to Companies Affected by Cyber Attacks and Data Breaches
- Is Your Business at Risk of a Data Breach?
- Using GREP,SED,and AWK commands
- Mountinga file to the virtual box
- Mounting afolder
- SORT command and pipes to combine multiple commands
b Scheduling Tasks
- Daemons
- Task scheduling in Linux
- Scheduling a job in Linux
- Cron and Crontab
- Using the AT command
Advanced Shell Scripting
- Why monitoring
- Process monitoring
- Top vs H Top
- What does PGREP do
- File and folder monitoring
- Monitoring tool inotifywait
- inotifywait options for folder monitoring
- Events of a folder in inotify
- FREE command
Database Connectivity
- Installing and configuring MySQL
- Securing MySQL
- Running queries from terminal
- Running queries from a shell script
Linux Networking
- What is networking in Linux
- Why do we need networking?
- Using networking commands
- Learning Firewall tools
Information over open source projects
- lynis(Unix-based auditing tool
- root kit hunter.
- What is Linux? Why Linux?
- History
Difference Between Linux and Windows
- Difference Between Linux and Unix
- GNU
- Usage
- Career Options
- Interesting Facts about Linux.
- 3 Why Linux is Virus proof?
- Various Linux Distributions.
- Pros and Cons
Root
- Who/why/what is root
Basic commands
- mkdir
- touch
- ls
- pwd
- cd
- chmod
- df
- du
- dd
- adduser
- sort
- passwd
- rm/rmdir
- date
- tar
- gzip
- top
Editors
a) Vi Editor
GNU/LINUX OS Installation
Basic System configuration and Administration.
OS Installation.
Understanding Files and Directories in Linux
- File Structure and hierarchy
- File Permissions
- LVM overview
Schedulers
- cron
- at
User Administration
Software Installation In Linux.
- RPM
- make
Linux Boot process
- Boot Loaders (LILO and GRUB)
- System Initialization
- inittab
- rc.sysinit
- rc
LVM (Logical Volume Manager)
- Volume groups
- Physical and logical volumes
- Resizing LVs etc
TCP/IP Network Management.
- route
- ifconfig
- ping
- netstat
Driver/Module Installation and Removal.
- modprobe
- rmmod
- insmod
- lsmod
- modinfo
Log Monitoring and rotating
OpenSSH - The GNU/Linux Secure Shell
- ssh
- Sshd
- Scp
sudo and su - Giving users SuperUser Privileges
Linux Administration.
- Single User Mode
- Rescue Mode
- IP Tables
- File Sharing with SAMBA
- NFS
- Mail Server using SENDMAIL
- Web Server installation (apache)
- Proxy Server installation using SQUID.
- Firewalling using iptables
- PAM (plug gable Authentication modules)
- Linux Performance Monitor
- SAR utility.
- Monitor cpu using sar
- track Application causing Memory Leak
Linux Hardening.
Linux Scripting
Introduction to Shell Scripting
- What is shell scripting?
- Types of shell
- Creating and writing a shell script
- Changing the permission of the shell script
- Executing the script
- Environment variables
- Defining a local and a global variable
- User input in a shell script
Conditional, Looping Statements and Functions
- What are Conditional statements
- IF, IF-ELSE, Nested IF statements
- What are Looping statements
- WHILE, UNTIL and FOR statements
- Using the case…esac statement
- Functions
- Information Security Threats and Attack Vectors
- Motives, goals, and objectives of information security attacks
- Top information security attack vectors
- Information security threat categories
- Types of attacks on a system
- Information Warfare
- Hacking Concepts
- What is hacking?
- Who is a hacker?
- Hacker classes
- Hacking phases
- Ethical Hacking Concepts
- What is Ethical Hacking?
- Why is Ethical Hacking necessary?
- Scope and limitation sof Ethical Hacking
- Skills of an Ethical Hacker
- Information Security Controls
- Information Assurance (IA)
- Information Security Management Program
- Enterprise Information Security Architecture (EISA)
- Network security zoning
- Defense-in-Depth
- Information security policies
- Physical Security
- What is risk?
- Threat modeling
- Incident management
- Security Incident and Event Management(SIEM)
- User Behaviour Analytics (UBA)
- Network security controls
- Identity and Access Management(IAM)
- Data leakage, backup, and recovery
- The role of AI/ML in Cyber Security
- Penetration Testing Concepts
- Why penetration testing?
- Security audit
- Vulnerability Assessment
- BlueTeaming/RedTeaming
- Types and phases of penetration testing
- Security Testing Methodology
- Information Security Laws and Standards
- Payment Card Industry Data Security Standard (PCI-DSS)
- ISO/IEC27001:2013
- Health Insurance Portability and Account ability Act(HIPAA)
- Sarbanes Oxley Act (SOX)
- The Digital Millennium Copyright Act(DMCA)
- Federal Information Security Management Act(FISMA)
- Cyber law in different countries
- Foot printing through Search Engines
- Foot print using advanced Google hacking techniques
- Information gathering using Google Advanced Search and Image Search
- Google Hacking Database
- VoIP and VPN Foot printing through Google Hacking Database
- Foot printing through Web Services
- Finding the company’ Stop-level Domains (TLDs) and sub-domains
- Finding the geographical location of the target
- People Search on social net working sites and people search services
- Gathering information from LinkedIn
- Gather information from financial services
- Foot printing through job sites
- Monitor in target using alerts
- Information gathering using groups, forums, and blogs
- Determining the OS
- VoIP and VPN Foot printing through SHODAN
- Foot printing through Social Networking Sites
- Collecting information through social engineer in gone social networking sites
- Website Foot printing
- Mirroring the entire website
- Extracting website information
- Monitoring web pages for updates and changes
- Email Foot printing
- Tracking email communications
- Collecting information from the email header
- Email tracking tools
- Competitive Intelligence
- Who is Foot printing
- Who is Lookup
- Who is Lookup result analysis
- Who is Lookup tools
- Finding IP geo location information
- DNS Foot printing
- Extracting DNS information
- DNS interrogation tools
- Network Foot printing
- Locate the net work range
- Traceroute
- Traceroute analysis and tools
- Foot printing Through Social Engineering
- Shoulder surfing
- Dumpster diving
- Foot printing Tools
- Maltego
- Recon-ng
- FOCA
- Recon-Dog
- OSR Framework
- Additional Foot printing tools
- Foot printing Counter measures
- Foot printing Pen Testing
- Introduction to Network Scanning
- Scanning tools: Nmap, Hping2/Hping3, and Hping commands
- Scanning Techniques
- ICMP scanning
- Ping sweep
- ICMP echo scanning
- TCP connect/full-open scan
- Stealth Scan/ half-open scan
- Inverse TCP flag scanning
- Xmas scan
- ACK flag probe scanning
- IDLE/IPID header Ssan
- UDP scanning
- SSDP and list scanning
- Port scanning counter measures
- Scanning Beyond IDS and Firewall
- IDS/Firewall Evasion Techniques
- Packet fragmentation
- Source routing
- IP address decoy
- IP addresss poofing
- Proxy servers
- Anonymizers
- Banner Grabbing
- How to identify target system OS
- Banner grabbing counter measures
- Draw Net work Diagrams
- Drawing network diagrams
- network discovery and mapping tools
- network discovery tools for mobile
- Scanning Pen Testing
- Enumeration Concepts
- What is Enumeration?
- Techniques for Enumeration
- Services and port state Enumerate
- Net BIOS Enumeration
- Net BIOS Enumeration tools
- Enumerating user accounts
- Enumerating shared resources using Net View
- SNMP Enumeration
- SNMP (Simple Network Management Protocol) Enumeration
- Working of SNMP
- Management Information Base (MIB)
- SNMP Enumeration tools
- LDAP Enumeration
- LDAP Enumeration tools
- NTP Enumeration
- NTP Enumeration tools
- SMTP and DNS Enumeration
- SMTP Enumeration
- SMTP Enumeration tools
- DNS Enumeration using zone transfer
- Other Enumeration Techniques
- IP sec Enumeration
- VoIP Enumeration
- RPC Enumeration
- Unix/Linux User Enumeration
- Enumeration Counter measures
- Enumeration Pen Testing
- Vulnerability Assessment Concepts
- What is vulnerability assessment?
- Vulnerability classification and research
- Vulnerability-Management Life Cycle
- Vulnerability Assessment Solutions
- Vulnerability scanning solutions
- Types of vulnerability assessment tools
- Choosing a vulnerability assessment tool
- Vulnerability Scoring Systems
- Common Vulnerability Scoring System (CVSS)
- Common Vulnerabilities and Exposures (CVE)
- National Vulnerability Database (NVD)
- Resources for Vulnerability Research
- Vulnerability Assessment Reports
- Analysing vulnerability scanning report
- System Hacking Concepts
- CEH Hacking Methodology (CHM)
- System hacking goals
- Cracking Passwords
- Password cracking
- Types of password attacks
- Password recovery tools
- Password salting
- Password cracking tools
- Escalating Privileges
- Privilege Escalation techniques
- How to defendagainst privilege escalation?
- Executing Applications
- Tools for executing applications
- Key logger
- Spyware
- Hiding Files
- Root kits
- NTFS Data Stream
- What is steganography?
- Covering Tracks
- Disabling auditing: Audit pol
- Clearing logs
- Clear online tracks
- Covering BASH shell tracks
- Covering tracks on the net work and OS
- Covering tracks tools
- Malware Concepts
- Introduction to malware
- Components of malware
- Trojan Concepts
- What is a trojan and it's types?
- Trojan horse construction kit
- Wrappers
- Crypters
- Evading Anti-virus techniques
- Virus and Worm Concepts
- Introduction to viruses
- Stages of virus life
- Different types of viruses
- Virus hoaxes
- Fake antiviruses
- Ransomware
- Creating virus
- Computer worms
- Worm makers
- Malware Analysis
- Introduction to malware analysis
- What is Sheep Dip Computer?
- Anti-virus sensor systems
- Malware analysis procedure
- Counter measures
- Trojan counter measures
- Backdoor counter measures
- Virusand worms counter measures
- Anti-Malware Software
- Anti-trojan software
- Antivirus software
- Malware Penetration Testing
- Sniffing Concepts
- Network sniffing
- Types of sniffing
- Hardware protocol analyzers
- SPAN port
- Wire tapping
- Lawful interception
- Sniffing Technique
- MAC attacks
- DHCP attacks
- ARP poisoning
- Spoofing attacks
- DNS poisoning
- Sniffing Tools
- Wire shark
- Wire shark filters
- Sniffing tools
- Packet sniffing tools for mobile
- Counter measures
- How to Defend Against Sniffing
- Sniffing Detection Techniques
- How to detect sniffing
- Promiscuous detection tools
- Sniffing penetration testing
- Social Engineering Concepts
- What is Social Engineering?
- Phases of Social Engineering attack
- Social Engineering Techniques
- Types of Social Engineering
- Human-based Social Engineering
- Computer-based Social Engineering
- Mobile-based Social Engineering
- Insider Threats
- Insider threat/insider attack
- Types of insider threats
- Social Engineering through impersonation on social networking sites
- Social networking threats to corporate networks
- Identity Theft
- Counter measures
- Social Engineering countermeasures
- Insider threats countermeasures
- Identity theft countermeasures
- Detect phishing emails
- Anti-phishing tool bar
- Common Social Engineering targets and defense strategies
- Social Engineering Pen Testing
- Social Engineering pen testing tools
- DoS/DDoS Concepts
- What is aDenial-of-Service attack?
- What is distributed Denial-of-Service attack?
- DoS/DDoS Attack Techniques
- Basic categories of DoS/DDoS attack vectors
- UDP, ICMP, and SYN flood attack
- Ping of death and smurf attack
- Fragmentation attack
- HTTP GET/POST and slow loris attacks
- Multi-vector attack
- Peer-to-peer attacks
- Permanent Denial-of-Service attack
- Distributedre flection Denial-of-Service (DRDoS)
- Botnets
- Organized cyber crime:organizational chart
- Botneteco system
- Botnet Trojans
- DDoS Case Study
- DDoS attack
- Hackers Advertise Links To Download Botnet
- Use of mobile devices asbotnets for launching DDoS attacks
- DDoS Case Study:Dyn DDoS Attack
- DoS/DDoS Attack Tools
- DoS and DDoS attack tool for mobile
- Counter measures
- Detection techniques
- DoS/DDoS counter measure strategies
- DDoS Attack counter measures
- Techniques to defend against botnets
- DoS/DDoS protectionat ISP Level
- DoS/DDoS Protection Tools
- Advanced DDoS protection appliances
- DoS/DDoS protection tools
- DoS/DDoS Penetration Testing
- Denial-of-Service (DoS) Attack Pen Testing
- Session HijackingConcepts
- What is session Hijacking?
- Session Hijackingprocess
- Types of Session Hijacking
- Packet analysis of a local session hi jack
- Session Hijackingin OSI Model
- Spoofing vs. Hijacking
- Application Level Session Hijacking
- Compromising session IDs using sniffingand by predicting session token
- Man-in-the-Middle attack
- Man-in-the-Browser attack
- Client-side attacks
- Cross-site script attack
- Compromising session IDs
- Session fixation
- Session Hijackingusing proxy servers
- CRIME attack
- forbidden attack
- Network Level Session Hijacking
- TCP/IP Hijacking
- IP spoofing: source routed packets
- RST Hijacking
- Blind Hijacking
- UDP Hijacking
- MiTM attack using for ged ICMP and ARP spoofing
- Session HijackingTools
- Session Hijackingtools
- Session Hijackingtools for mobile
- Counter measures
- Session Hijackingdetection methods
- Protection against session Hijacking
- Session Hijackingdetection and prevention tools
- IPSec
- Penetration Testing
- IDS, Firewall and Honeypot Concepts
- Intrusion Detection System (IDS)
- Firewall
- Honeypot
- IDS, Firewall and Honeypot Solutions
- Intrusion detection tool
- Firewalls and honeypot tools
- Evading IDS
- IDS/firewall evasion tools and techniques
- Packet Fragment Generator Tools
- Detecting Honeypots
- Detecting and defeating honeypots
- Honeypot detection tool: Send-Safe Honeypot Hunter
- IDS/Firewall Evasion Counter measures
- How to defend against IDS evasion
- How to defend against firewall evasion
- Firewall/IDS Penetration Testing
- Web Server Concepts
- Web server operations
- Open source web server architecture
- IIS web server architecture
- Web server security issue
- Web Server Attacks
- DoS/DDoS attacks
- DNS server Hijacking
- DNS amplification attack
- Directory traversal attacks
- Man-in-the-Middle/sniffing attack
- Phishing attacks
- Website defacement
- Web Server misconfiguration
- HTTP response splitting attack
- Web cache poisoning attack
- SSH brute force attack
- Web server password cracking
- Web Server Attack Methodology
- Information gathering
- Web server Foot printing/banner grabbing
- Website mirroring
- Vulnerability scanning
- Session Hijacking
- Web server passwords hacking
- Web Server Attack Tools
- Meta sploit
- Webserver attack tools
- Counter measures
- Web servers in separate secure server security segment
- Counter measures
- Detecting web server hacking attempts
- HTTP response splitting
- Web cache poisoning
- DNS Hijacking
- Patch Management
- What is patch management
- Patches And Hotfixes
- Installation Of Patch
- Patch management tools
- Web Server Security Tools
- Web application security scanners
- Web server security scanners
- Web server security tools
- Web Server Pen Testing
- Web server penetration testing
- Web server pen testing tools
- WebApp Concepts
- Introduction to web applications
- Web application architecture
- Web2.0 applications
- Vulne rability stack
- WebApp Threats
- OWASP Top 10 Application Security Risks
- Web apphacking methodology
- Foot print web Infrastructure
- Analyze web applications
- Bypass client-side controls
- Attack authentication mechanism
- Attack authorization schemes
- Attack accesscontrols
- Attack session management mechanism
- Perform injection/input validation attacks
- Attack application logic flaws
- Attack database connectivity
- Attack web appclient
- Web App Hacking Tools
- Counter measures
- Web application fuzz testing
- Source code review
- Encoding schemes
- Defend against injection attacks
- Web application attack counter measures
- Defend against web applicatio nattacks
- WebApp Security Testing Tools
- Web application security testing tools
- Web application firewall
- WebApp Pen Testing
- Web application pen testing
- Web application pen testing framework
- SQL Injection Concepts
- What is SQL injection?
- SQL injection and server-side technologies
- HTTP POST Request
- Normal SQL Query
- SQL Injection Query
- Code Analysis
- Types of SQL Injection
- SQL Injection Methodology
- SQL Injection Tools
- SQL power injector and SQL map
- The mole and SQL injection
- SQL injection tools for smobile
- Evasion Techniques:
- Evading IDS
- Types of signature evasion techniques:
- In-line comment
- Charen coding
- String concatenation
- Obfuscated codes
- Manipulating white spaces
- Hexen coding
- Sophisticated matches
- URL encoding
- Null Byte
- Case variation
- Declare variable
- IP fragmentation
- Counter measures
- Defend against SQL injection attacks
- SQL injection detection tools
- Wireless Concepts
- Wireless terminologies, networks, and standards
- Service Set Identifier (SSID)
- Wi-Fi Authentication modes
- Wi-Fi Authentication process using a centralized authentication server
- Types of wireless antennas
- Wireless Encryption
- Types of wireless encryption
- WEP v/s WPA vs.WPA2
- WEP issues
- Weak Initialization Vectors (IV)
- Wireless Threats
- Rogue access point attack
- Client disassociation
- Misconfigured access point attack
- Unauthorized association
- Ad-Hoc Connection Attack
- Honey pot access point attack
- APMAC spoofing
- Denial-of-Service attack
- Key Reinstallation Attack (KRACK)
- Jamming signal attack
- Wireless Hacking Methodology
- Wi-Fi Discovery
- GPS mapping
- Wireless traffic analysis
- Launch wireless attacks
- Crack Wi-Fi Encryption
- Wireless Hacking Tools
- WEP/WPA cracking tools
- WEP/WPA cracking tool for mobile
- Wi-Fi Sniffer
- Wifi Traffic Analyzer tools
- Other wireless hacking tools
- Bluetooth Hacking
- Bluetooth stack
- Bluetooth hacking
- Bluetooth threats
- How to blue Jack a victim
- Bluetooth hacking tools
- Counter measures
- Wireless security layers
- How to defend against WPA/WPA2 cracking, KRACK attacks, wireless attacks, and Bluetooth hacking
- How to detect and block rogue AP
- Wireless Security Tools
- Wireless intrusion prevention systems
- Wireless IPS deployment
- Wi-Fi security auditing tools
- Wi-Fi predictive planning tools
- Wi-Fi vulnerability scanning tools
- Bluetooth security tools
- Wi-Fi security tools for mobile
- Wireless Pen Testing
- Wireless Penetration Testing
- Wireless Penetration Testing Framework
- Mobile Platform Attack Vectors
- Vulnerabilities in mobile business environment
- OWASP top 10 mobile risks
- Anatomy Of A mobile attack
- Mobile attack vectors
- Mobile platform vulnerabilities
- Security issues arising from App stores
- Apps and boxing issues
- Mobile spam
- SMS Phishing Attack (SMiShing)
- Hacking Android OS
- Android OS and rooting
- Blocking Wi-Fi access using Net Cut
- Hacking with z ANTI
- Hacking network using Network Spoofer
- Launching DdoS attack using Low Orbit Ion Cannon (LOIC)
- Performing session Hijacking using Droid Sheep
- Hacking with Orbot Proxy
- Android-based sniffer
- Android trojans
- Securing android devices
- Android security tools
- Android device tracking tools
- Hacking iOS
- Apple iOS
- Jail breaking iOS
- iOS trojans
- Guidelines for securing iOS devices
- iOS device security and tracking tools
- Mobile Spyware
- mSpy
- Mobile Device Management
- Mobile Device Management (MDM)
- MDM solutions
- Bring Your Own Device (BYOD)
- Mobile Security Guidelines and Tools
- General guidelines for mobile platform security
- Mobile device security guidelines for Administrator
- SMS phishing counter measures
- Mobile protection tools
- Mobile anti-spyware
- Mobile Pen Testing
- Android Phone Pen Testing,
- iPhone Pen Testing,
- Mobile Pen Testing Toolkit: Hackode
- IoT Concepts
- What is IoT?
- How does IoT work?
- IoT architecture
- IoT application are as and devices
- IoT technologies and protocols
- IoT communication models
- Challenges of IoT
- Threat vs opportunity
- IoT Attacks
- IoT security problems
- OWASP top 10 IoT vulnerabilities and obstacles
- IoT attack surface areas
- IoT threats
- Hacking IoT devices
- IoT attacks
- Case Study: Dyn Attack
- IoT Hacking Methodology
- What is IoT device hacking?
- IoT hacking methodology
- IoT hacking tools
- Information gathering tools
- Sniffing Tools
- Vulnerability scanning tools
- Counter How to defend against IoT hacking measures
- How to defend against IoT hacking
- General guidelines for IoT device manufacturing companies
- OWASP Top 10 IoT vulnerabilities solutions
- IoT framework security considerations
- IoT security tools
- IoT Penetration Testing
- Cloud Computing Concepts
- Introduction to cloud computing
- Separation of responsibilities in cloud
- Cloud deployment models
- NIST cloud deployment reference architecture
- Cloud computing benefits
- Virtualization
- Cloud Computing Threats
- Cloud Computing Attacks
- Service Hijacking using Social Engineering attacks
- Service Hijacking using network sniffing
- Session Hijacking using XSS attack
- Session Hijacking using session riding
- Domain Name System (DNS) attacks
- Side channel attacks cross-guest VM breach
- SQL Injection attacks
- Cryptanalysis attacks
- Wrapping attack
- DoS and DDoS attacks
- Man-in-the-Cloud attack
- Cloud Security
- Cloud security control layers
- Cloud computing security considerations
- Placement Of Security Controls in the cloud
- Best practices for securing cloud
- NIST recommendations for cloud security
- Organization/Provider cloud security compliance checklist
- Cloud Security Tools
- Cloud Penetration Testing
- What is cloud pen testing?
- Key considerations for pen testing in the cloud
- Recommendations for Cloud Testing
- Cryptography Concepts
- Cryptography
- Types of cryptography
- Government Access to Keys (GAK)
- Encryption Algorithms
- Ciphers
- Data Encryption Standard (DES)
- Advanced Encryption Standard (AES)
- RC4, RC5, and RC6 algorithms
- Two fish
- The DSA and related signature schemes
- Rivest Shamir Adleman (RSA)
- Diffie-Hellman
- Message digest (One-WayHash) functions
- Cryptography Tools
- MD5 hash calculators
- Cryptography tools
- Cryptography tools for mobile
- Public Key Infrastructure (PKI)
- Public Key Infrastructure (PKI)
- Certification authorities
- Signed certificate (CA) vs. self-signed certificate
- Email Encryption
- Digital signature
- Secure Sockets Layer (SSL)
- Transport Layer Security (TLS)
- Cryptography toolkit
- Pretty Good Privacy (PGP)
- Disk Encryption
- Disk encryption
- Disk encryption tools
- Cryptanalysis
- Cryptanalysis methods
- Code Breaking Methodologies
- Cryptography attacks
- Online MD5 decryption tools
- Counter measures: How to Defend Against Cryptographic Attacks
- Security Administrators
- Network Security
- Cyber Security Audit
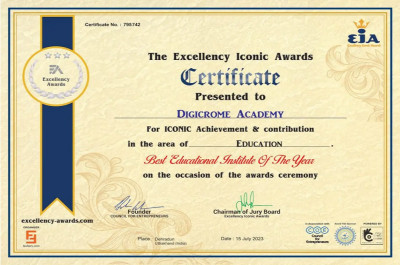
Our Certificates
Certified by